The aim of this Construction of wireless matchbox for digital lantern using RF technology project is to control a high voltage electrical lamp control operation with the help of RF. The status of lamp control either ON/OFF can be observed on receiver side with the indication of LED. Users can control the lamp operation with the help of control buttons.
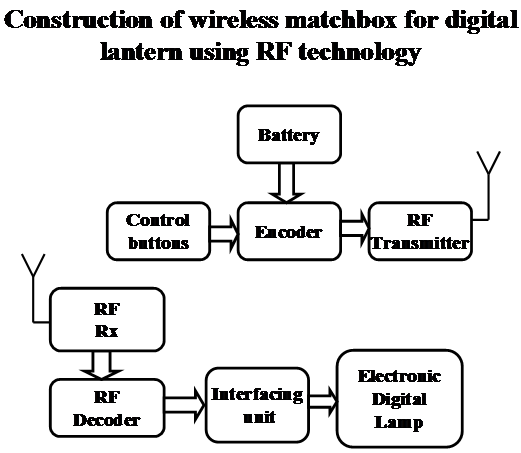
This Construction of wireless matchbox for digital lantern using RF technology project consists of an input from control buttons it sends the appropriate signals from RF transmitter, then the receiver receives the signals and performs the operation either to ON/OFF the lamp. Then it processes the data and takes necessary action and updates the status through LED.
User can simply ON/OFF the device with the help of remote communication.
Features:
1. Aims at energy conservation.
2. Provides user friendly interface.
3. Provides fast access to using RF.
The project provides learning’s on the following advancements:
1. Interfacing RF to control buttons.
2. Lamp control circuitry.
Block Diagram: