About the project:
BPO (Business Process Outsourcing) is an outsource partner take responsibility for providing back office support for a client organization. The main benefits of BPO for any organization are:
- Reducing Costs
- Improving Service
- Transferring Risk
Processing Services: BPO’s system design based on our wide knowledge of hardware and software, supported by an efficient domain and Process oriented staff ensures document processing capability with:
- Efficient data capture
- High accuracy levels
- On schedule delivery
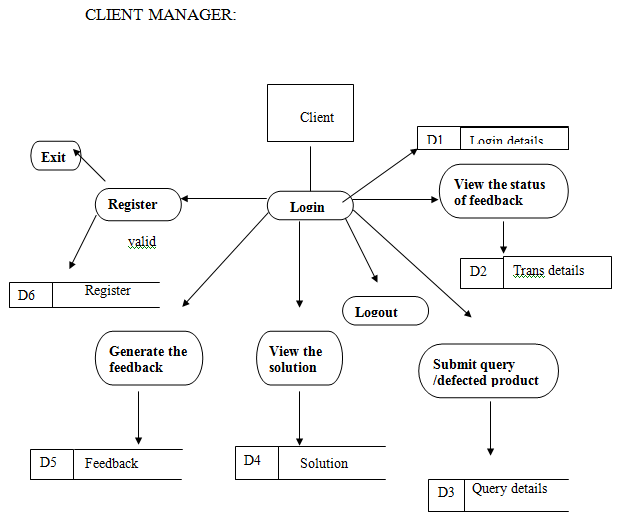
This project entitled “Intelligent Business Process Manager” is a client server based administrative software utility to manager and automates various processes taking place in a business processing and outsourcing company mainly focused on data conversion. It consists of three software components, Server Manager, Client Assistant, QC Assistant. Each component can operate independently and can communicate with each other using TCP/IP Protocol. The three components of the IBPM operate accordingly to coordinate the various process-taking places in a BPO firm.
Server Manager
The Server Manger is the core components of the IBPM.
The Server Manager starts listening the remote client’s request to establish a connection.
After checking the security privileges of the user, the server Manager establishes a dedicated connection to the requested client using TCP/IP Protocol and creates a separate system thread to manage the newly established connection.
The administrator can deploy works and reworks to the remote users through this Server Manager.
The Server Manager also allows the administrator to create backup of the deployed work in the server at various stages of its progress.
If a failure occurs I any one of the remote user’s computer the Server Manager can re-deploy the work from the server’s backup to that particular user.
Client Assistant
Client Assistant is a software component for those users who are actually in the data conversion process.
A separate copy of the Client assistant software is required on each user’s system.
Users are logged in to the Server Manager through the Client Assistant.
The Client Assistant use TCP/IP protocol to establish a connection to the Server Manager component running in the remote server.
When a user is successfully logged into the Server Manager the administrator can schedule and deploy the wok to that specific user.
When a user completes his work, he can upload it the server through the Client Assistant.
Quality Controller
QC Assistant is a software component for Quality Controllers, who verifies the quality of the finished work submitted by the users to the Server Manager.
A separate copy of the QC Assistant is required for each Quality Controller System.
QC-Users are logged into the Server Manager through the QC Assistant.
The QC Assistant use TCP/IP protocol to establish a connection to the Server Manager Component running in the remote server.
When a QC-User is successfully logged in to the Server Manager, the administrator can schedule and deploy the finished work from different users to the Quality Controller for quality checking.
SYSTEM ANALYSIS AND DESIGN
Analysis of the system
The system is for simplifying the communication difficulties between different of an organization.
What does our organization want to share between its branches?
Declaring any information regarding business to its branch managers.
Sharing details about their products and discussing about services.
Declaring any instructions to its staff working at different branches.
Interfacing Human resources and administration.
These functions are divided into three categories they are:
- Server Manager
- Client Assistant
- Quality Controller
Server Manager
The server Manager starts listening the remote the client’s request to establish a connection. After checking the security privileges of the user, the Server Manager establishes a dedicated connection to the requested client using TCP/IP Protocol and creates a separate system thread to manage the newly established connection.
Client Assistant
Client Assistant is a software component for those users who are actually in the data conversion process. A separate copy of the Client Assistant software is required on each user’s system. Users are logged into the Server Manager through the Client Assistant. The Client Assistant use TCP/IP protocol to establish a connection to the server manager component running in the remote server.
Quality Controller
Who verifies the quality of the finished work submitted by the users to the server manager? A separate copy of the QC Assistant is required for each Quality Controller’s system. QC-Users are logged into the Server Manager through the QC Assistant. The QC Assistant use TCP/IP protocol to establish a connection to the Server Manager Component running in the remote server.
DATABASE DESIGN
Database is a collection of information related to a particular subject or purpose. This design provides the detailed structure of the table layout.
Database design consists of the following tables:
1. Table Name : Login
Primary Key : userid
| Field Name | Type | Description |
| User Name | Varchar (20) | Login User Name |
| Password | Varchar (10) | Login Password |
2. Table Name : Registration
Primary Key : E-Mail id
| Field Name | Type | Description |
| Name | Varchar (15) | User Name |
| Gender | Char (7) | Gender |
| Id | Varchar (10) | E-Mail Id |
| Pass | Varchar (7) | Password |
| RePass | Varchar (7) | Retype Password |
| Dob | Varchar (10) | Date Of Birth |
| State | Char (7) | State |
| City | Char (8) | City |
| PhNo | Varchar (10) | Phone No |
| Occu | Char (12) | Occupation |
3. Table Name : Compliant
Primary Key : Compliant id
| Field Name | Type | Description |
| Compl_ID | Varchar (10) | Complaint ID |
| Cust_ID | Varchar (10) | Id of customer |
| Cust_ Name | Char (20) | Name of customer |
| Compl_Date | Date (7) | Complaint Date |
| Compl_ Time | Time (7) | Complaint Time |
| Compl_ Type | Char (15) | Type Of Complaint |
| Desc_Compl | Char (10) | Description of complaint |
4. Table Name : Compliant Transfer
Primary Key : Compliant Transfer id
| Field Name | Type | Description |
| Compl_ Transfer ID | Varchar (10) | Transfer id of Complaint |
| Compl_ ID | Varchar (15) | Id of Complaint |
| Compl_ Date | Date (10) | Complaint Date |
| Compl_ Time | Time (10) | Complaint Time |
| CA_ ID | Varchar (15) | Client Assistant ID |
| Status Flag | Boolean (15) | Transfers Status |
5. Table Name : Pending Complaint
Primary Key : Compliant id
| Field Name | Type | Description |
| Complaint ID | Varchar (15) | Complaint ID |
| Client Name | Char (20) | Name of Client |
| Client ID | Varchar (15) | ID of Client |
| Complaint Date | Date (10) | Complaint Date |
| Complaint Time | Time (10) | Complaint Time |
| Solution | Char (15) | Solution |
6. Table Name : Client Assistant
Primary Key : Client Assistant id
| Field Name | Type | Description |
| CA_ID | Varchar (15) | ID of Client Assistant |
| CA_Name | Char (20) | Name of Client Assistant |
| CA_Address | Varchar (25) | Address of Client Assistant |
| CA_System ID | Varchar (10) | System ID of Client |
| CA_Specialization | Char (15) | Specialization of Client Assistant |
7. Table Name : Quality Controller
Primary Key : Quality Controller id
| Field Name | Type | Description |
| QC_ID | Varchar (15) | ID of Quality Controller |
| QC_Name | Char (20) | Name of Quality Controller |
| QC_Address | Varchar (20) | Address of Quality Controller |
| QC_Phone No | Number | Phone No of Quality Controller |
| Varchar | E-Mail Id of Quality Controller |
8. Table Name : Solution
Primary Key : Solution id
| Filed Name | Type | Description |
| Solution ID | Varchar (15) | ID of Solution |
| Solution | Char (15) | Solution |
| Complaint Transfer ID | Varchar (9) | Complaint Transfer ID |
| Solution Date | Date (10) | Solution Date |
| Solution Time | Time (10) | Solution Time |
9. Table Name : Feedback
Primary Key : Client id
| Field Name | Type | Description |
| Client Id | Varchar (10) | ID of Client |
| Client Name | Char (20) | Name of Client |
| Client Phone No | Number (15) | Phone No of Client |
| Client Address | Varchar (20) | Address of Client |
| Client E-Mail | Varchar (20) | E-Mail id of Client |
| Feedback | Varchar (15) | Description of feedback |
CONCLUSION:
The project ‘Network Packet Sniffer’ is meant for providing security to a system by forwarding the validated packet details to the firewall. The system is developed in VC++ as front-end tool and Oracle 8i as backend tool.
The Remote Monitoring System project can be thus found to be useful in various applications in both home use as well as office use to detect unnoticed malpractices in our system. Thus it makes the user to be careful about the improper usage of his system thus enabling him to take appropriate actions to stop them. Hence he can have a control over his system even in his absence. Hence it provides a level of security to the administrator’s PC. Remote Monitoring System is a powerful monitoring and surveillance tool that is useful on all platforms. This project helps us in a networking environment to monitor and spy all the system in the network connection without knowing the user.


plese send me this project
Please send me the source code of this project : Inteligent Bussines Process Manager
project
Please send me source code for this project
Send me a source code of project
Intelligent process business manager