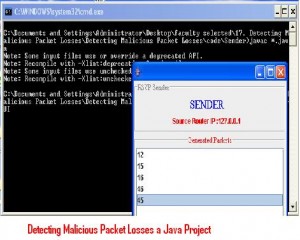
Detecting Malicious Packet Losses a Java Project is for B.tech computer science final year students who are interested in implementing java related projects.
Description:
Network routers occupy a unique role in modern distributed systems. They are responsible for cooperatively shuttling packets amongst themselves in order to provide the illusion of a network with universal point-to-point connectivity. However, this illusion is shattered – as are implicit assumptions of availability, confidentiality, or integrity – when network routers are subverted to act in a malicious fashion.
By manipulating, diverting, or dropping packets arriving at a compromised router, an attacker can trivially mount denial-of-service, surveillance, or man-in-the-middle attacks on end host systems. Consequently, Internet routers have become a choice target for would-be attackers and thousands have been subverted to these ends.
Advantages:
The solution is taken to detect whether a compromised router is maliciously manipulating its stream of packets. In particular, the system is concerned with a simple yet effective attack in which a router selectively drops packets destined for some Victim.
Unfortunately, it is quite challenging to attribute a missing packet to a malicious action because normal network congestion can produce the same effect. Modern networks routinely drop packets when the load temporarily exceeds their buffering capacities.
Previous detection protocols have tried to address this problem with a user-defined threshold: too many dropped packets imply malicious intent. However, this heuristic is fundamentally unsound; setting this threshold is, at best, an art and will certainly create unnecessary false positives or mask highly focused attacks.
Conclusion:
The designed, developed, and implemented system is a compromised router detection protocol that dynamically infers, based on measured traffic rates and buffer sizes, the number of congestive packet losses that will occur. Once the ambiguity from congestion is removed, subsequent packet losses can be attributed to malicious actions. We have tested our protocol in Emulab and have studied its effectiveness in differentiating attacks from legitimate network behavior.

anyone interested in buying this project at much cheaper rate can contact me on ravi.danny23@gmail.com 🙂
Please communicate through email only.