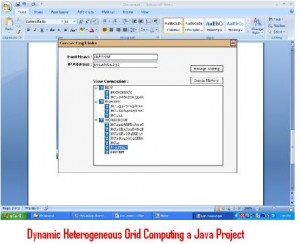
Dynamic Heterogeneous Grid Computing a Java Project is for computer science final year students who are interested in grid computing java project.
Description:
Communication Induced Check-pointing protocols usually make the assumption that any process can be check-pointed at any time. An alternative approach which releases the constraints of always check-point able processes, without delaying, “Any do not message reception” or altering message ordering enforcement by the communication layer and by the application.
Reason for implementation and others:
This protocol has been implemented within Pro-Active, an open source Java middle ware for asynchronous and distributed objects implementing the ASP (Asynchronous Sequential Processes).However, large applications executing on Grid or cluster architectures consisting of hundreds or thousands of computational nodes create problems with respect to reliability.
A Glittering Problem:
The source of the problems is node failures and the need for dynamic configuration over extensive runtime.
Conclusion:
By allowing recovery even under different numbers of processors, the approaches are especially suitable for applications with a need for adaptive or reactionary configuration control. The low-cost protocols offer the capability of controlling or bounding the overhead. A formal cost model is presented, followed by an experimental evaluation. It is shown that the overhead of the protocol is very small, and the maximum work lost by a crashed process is small and bounded.
The solution to this is two fault-tolerance mechanisms called Theft-Induced Check pointing and Systematic Event Logging. These are transparent protocols capable of overcoming problems associated with both benign faults, i.e., crash faults, and node or subnet volatility. Specifically, the protocols base the state of the execution on a data flow graph, allowing for efficient recovery in dynamic heterogeneous systems as well as multi threaded applications.
