Proposing system design: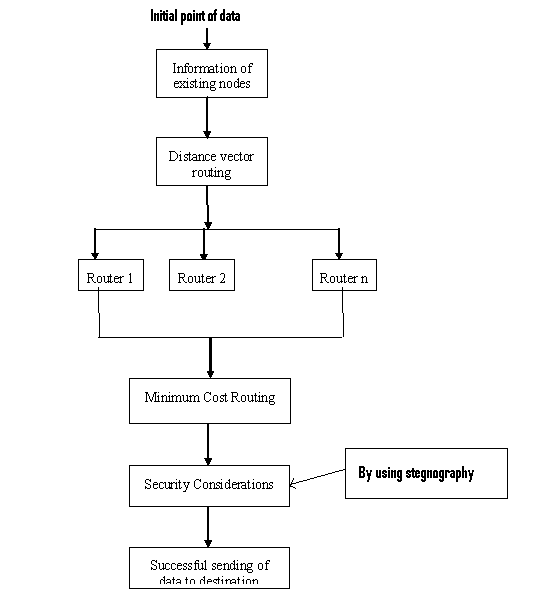
The modules which I consider come in this proposed design flow diagram.
- Terminal end or client will send the data to the destination end through the network medium.
- Every node has information about the all the terminals in the network, so it will establish the route according to the hop table.
- By using the distance vector algorithm, it will establish the route dynamically. It is possible by maintain the routing table information update periodically. Routers in the networks are updated with the routing and minimal cost of nodes, for periodical duration.
- In the next level, data packets are dynamically sent in different routes where the two consecutive packets never go through a one route.
- Next level, minimize the routing strategy by reducing the cost effects for routing.
- Security comes in this step to protect the data from the attacker, for that we are using the stegnography concept which makes the data in to hidden format by sending it to image.
- At the destination end, all the data packets are clustered as per the sequence number in the data packets.
This Paper is written & submitted by Chandu.
