In this thesis, we have suggested and studied IDPF architecture as an efficient countermeasure for the IP spoofing based DDoS attacks. IDPFs depend on BGP update messages interchanged on the Internet to conclude the validity of source address of a packet send by a neighbor.
We have demonstrated that IDPFs can easily be deployed on the present BGP based Internet routing architecture. We learned the conditions under which the IDPF framework can properly work without discarding any legitimate packets. IDPFs in an important manner limit the spoofing capability of attackers. In addition, they also assist to pinpoint the true origin of an attack packet to be within a small number of candidate networks, thus simplifying the reactive IP traceback process.
 The attached Constructing IDPFs using BGP Project Contains the below:
The attached Constructing IDPFs using BGP Project Contains the below:
TABLE OF CONTENT
ABSTRACT
ACKNOWLEDGMENT
TABLE OF CONTENT
LIST OF FIGURES
LIST OF TABLES
LIST OF ACRONYMS
Chapter 1: Introduction to the Project
1.1 History of the Project
1.2 Proposed System
1.3 Aims and Objectives of the Project
1.4 TCP and IP Protocol
1.5 How Spoofing works
1.5.1 Uses of Spoofing
1.5.2 Spoofing purpose
1.6 Conclusion
Chapter 2: Types of Spoofing
2.1 DDOS Attacks
2.2 Non-Blind Spoofing
2.3 Blind Spoofing
2.4 Man in the middle attack
Chapter 3: Security Requirements
3.1 Network security requirements
3.2 System security requirements
3.3 Information Security requirements
3.4 Conclusion
Chapter 4: Threats on data
4.1 Hackers
4.2 Vulnerability
4.3 Viruses
4.4 Trojan horse programs
4.5 Attacks
4.6 Conclusion
Chapter 5: Security Policies
5.1 What are policies?
5.2 Firewalls
5.3 Encryption
5.4 Intrusion Detection
5.5 Conclusion
Chapter 6: Review on BGP Protocol
6.1 Background
6.2 BGP Operations
6.2.1 Interautonomous system routing
6.2.2 Intra-autonomous system routing
6.2.3 Pass-through autonomous system
6.3 BGP Routing
6.4 BGP Message Types
6.4.1 Open message
6.4.2 Update message
6.4.3 Notification message
6.4.4 Keep-alive message
6.5 Conclusion
Chapter 7: BGP and AS interconnections
7.1 Policies and Route Selection
7.2 AS Relationships and Routing Policies
7.3 Conclusion
Chapter 8: IDPF Architecture
8.1 IDPF Overview
8.2 Constructing IDPFs
8.2.1 Correctness of IDPF
8.2.2 Routing policy complications
8.3 Practical Deployment of IDPF
8.4 Conclusion
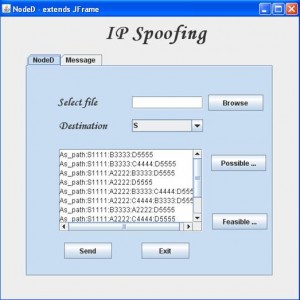
Chapter 9: Design and Implementation
9.1 Technologies Used
9.1.1 Javax.swing
9.1.2 Java.io package
9.1.3 Java.net package
9.1.4 Java.sql package
9.1.5 Java.awt package
9.2 Tools Used
9.2.1 Jframe Builder Tool
9.3 Code Snippet
9.4 Screen shots
Chapter 10: Conclusion and Future work of the Project
References to the Project
Download CONSTRUCTING INTER-DOMAIN PACKET FILTERS BASED ON BGP UPDATES TO CONTROL IP SPOOFING Java Final Year Project with source code.


plz i would kindly request you to get me this project with its all related information. thanks