Introduction to Typing pattern project:
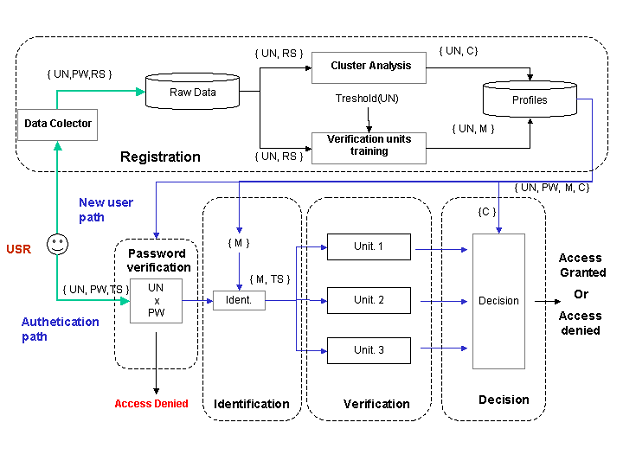
Typing pattern project explains about a concept of developing a secured password authentication system which works on keystroke bio metrics. In present scenario there are many password based access systems which have become more acute.
There are many researches carried out for providing best security method for password systems. In this project we explain about new technology called biometric keystroke which works on identifying individual based on their typing characteristics. Most of the applications which are developed to solve this problem having many issues like burden in logging procedure or tough to remember passwords.
This technology is used in news reporting system to find out who had sent the news and detect the person.
In this project report students can find more details on data flow diagram, uml diagrams, and architecture diagrams.
For more information on this topic students can download project report from below download link.