Decision of Destination:
Deciding the required destination is really the important task to be considered in this MS Project Dissertation and the coding used to achieve this is explained here. To decide the destination based on the time functionalities, a separate class named Destination is created and this class extends a predefined class known as TimerTask and this class is available with the java.Util package.
This class decides the destination based on the time during the execution and thus the timer object is used in this case. The actual process of deciding the destination is really a networking task and the Socket classes are used to decide the destination. A separate connection to the server is used this socket object. ServerSocket class is used for this purpose and thus once the connection to the server is established, now the destination is said to be decided and the server socket connection is set to be ready till the process is completed.
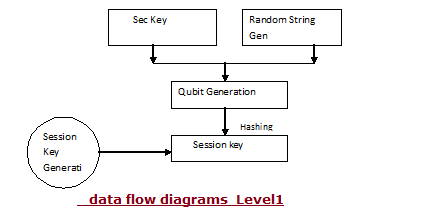
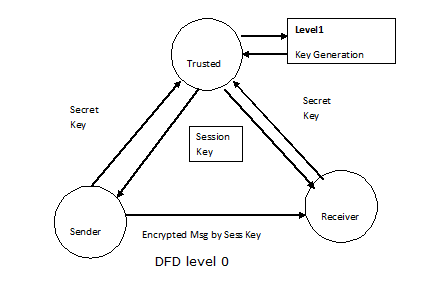
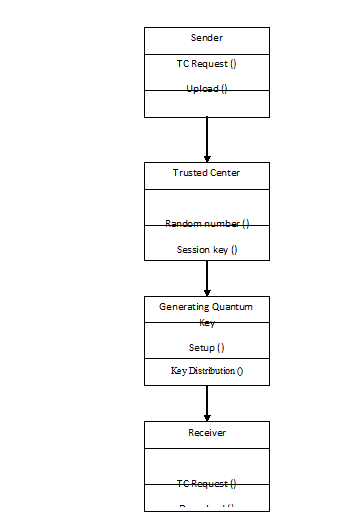
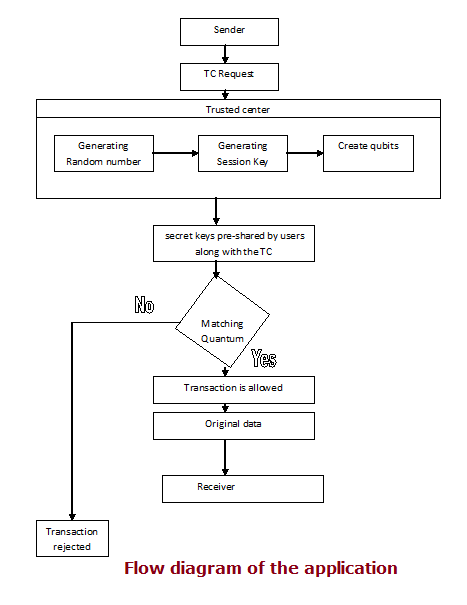
Once the connection to the server is established, now the message is chipper and sends to the receiver using the function known as receiver and now the messages are send in the form of chippers to the receivers. To ensure the secure communication, port numbers are used and thus the port based secure communication model is coded in this project. A separate set of session keys are used in this case and now the encryption and decryption algorithms can be used to distribute these keys.
The corresponding messages are encrypted and decrypted using this session keys and now the communication process can be said as successful and secure enough. The actual coding used to achieve this task is given in the Appendix section.
This Paper is written & submitted by Vamshidhar A.