UML Diagrams of Mobile Management System
The unified modeling language is a language for specification, constructing, visualizing and documenting the software and its components.
The UML is a graphical language with set of rules and syntaxes. The goal of UML is to keep the modeling simple.
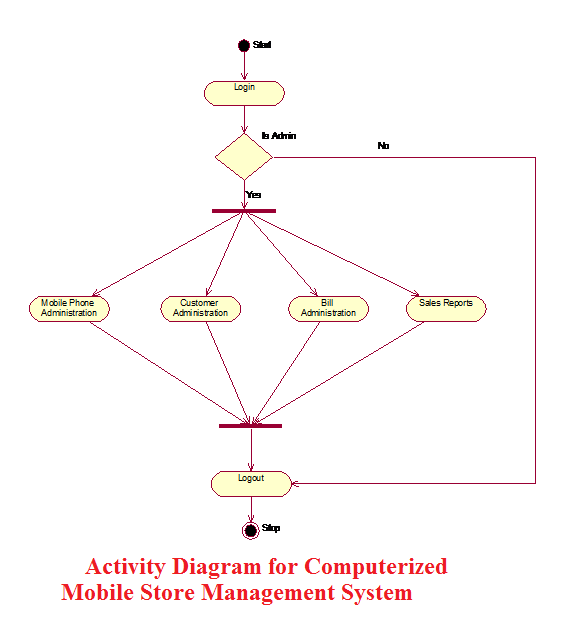
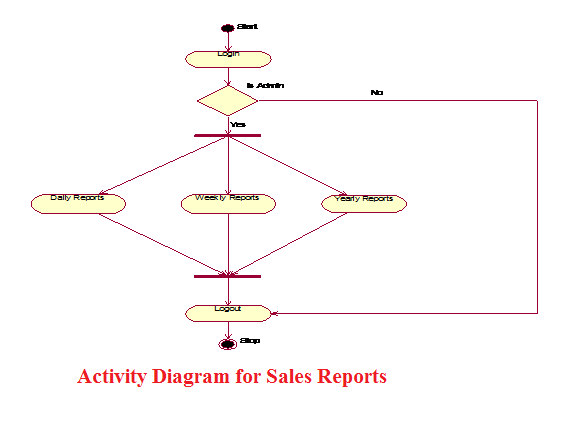
ACTIVITY DIAGRAM
Activity diagram is used to model an entire business process. The purpose of the E-R Diagram and activity diagram is below.
Activity Diagram for Computerized Mobile Store Management System
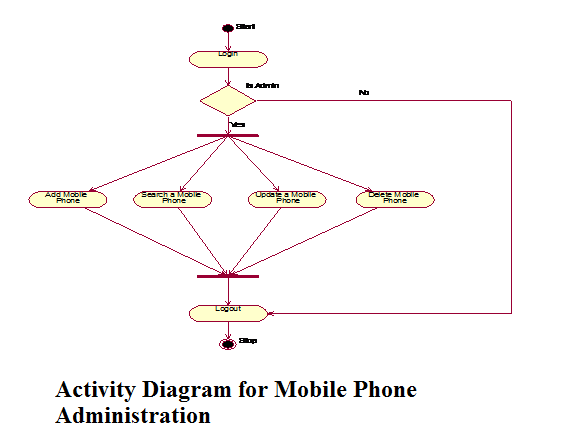
Activity Diagram for Mobile Phone Administration
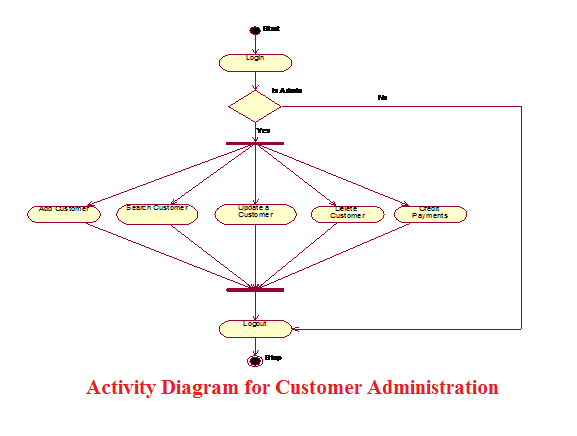
Activity Diagram for Customer Administration
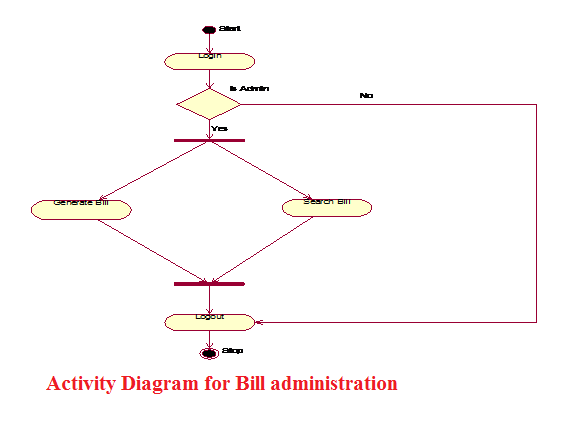
Activity Diagram for Bill administration
Activity Diagram for Sales Reports
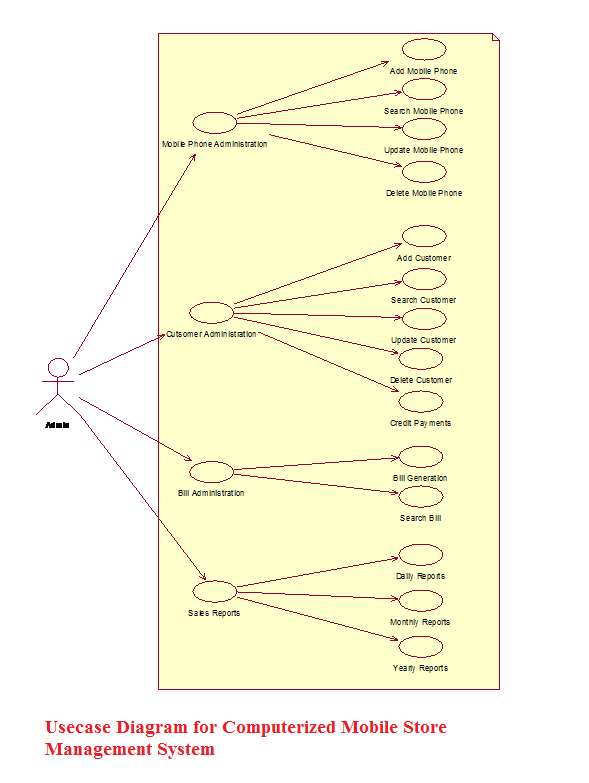
USE CASE DIAGRAM
Usecase Diagram for Computerized Mobile Store Management System.
Use Case Descriptions
- Mobile Phone Administration:
In the “Mobile Phone Administration” the Administrator adds, updates, searches, and deletes the Mobile Phones details on his system.
Add a new Mobile Phone:
Here the administrator adds the new Mobile Phones into his system. Here administrator enters the Mobile details like MobileId, MobileModel, Mobile Price, Mobile Phone Color, etc.
Search for a Mobile Phone:
Here the administrator searches a Mobile Phone details by entering the input like Mobileid, Mobile Phone, and Price.
Update a Mobile Phone Details:
Here the Administrator Updates the Mobile Phone details by modifying the Mobile Phone details.
Delete a Mobile Phone:
Here the Administrator Deletes a Phone details by entering the details like MobileId or IMEI no.
- Customer Administration:
In the “Customer Administration” the administrator adds, updates, searches, and deletes the customer details on his system.
Add a new Customer:
Here the administrator adds the new Customer details into his system. Here administrator enters the Customer Name, Customer Address, Mobile purchased, MobileId etc.
Search for a Customer:
In the ‘Search for a Phone’ system the administrator searches a Customer details by entering the input like CustomerId, Customer Name.
Update a Customer Details:
In the ‘Update a Customer Details’ system the administrator Updates the details by modifying the details like Customer Address, Customer credit details.
Delete a Customer:
In the ‘Delete a Customer’ system the administrator Deletes a Customer Details by entering input like CustomerId.
- Bill Administration:
In the “Bill Administration” the administrator generates and searches the bills.
Generate a Bill:
Here the Administrator generates the bill for sold Mobiles. Here he enters the information like Customer Name, Customer Address, Mobile Purchased, MobileId.
Search for a Bill:
Here the Administrator searches the bills by entering the details like Billid.
- Sales Reports:
In the “Sales Reports” the administrator can generate the Sales Reports for daily, monthly and yearly.
Daily Reports:
Here the Administrator can generate the Daily Sales Reports by giving the input information like Date on which the Sales Reports are needed.
Monthly Reports:
Here the Administrator can generate the Monthly Sales Reports by giving the input information like Month and Year on which the Sales Reports are needed.
Yearly Reports:
Here the Administrator can generate the Yearly Sales Reports by giving the input information like Year on which the Sales Reports are needed.
SEQUENCE DIAGRAM
Sequence Diagram For Computerized Mobile Store Management System
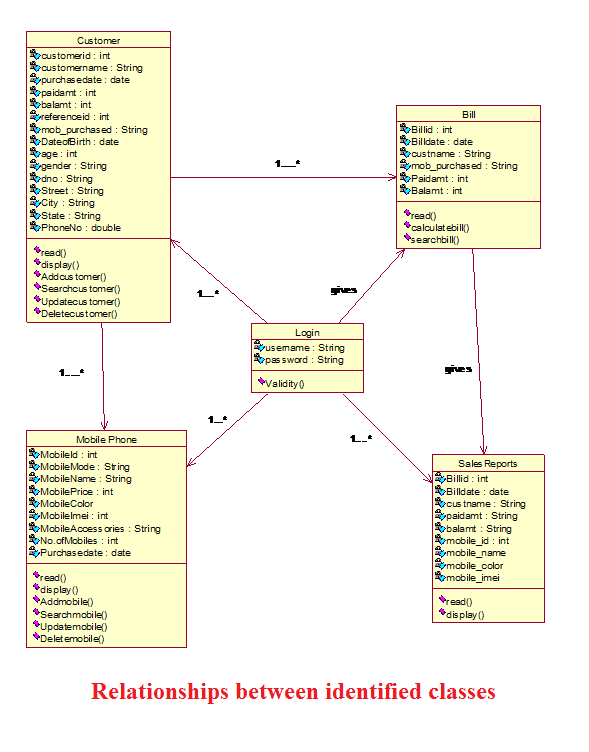
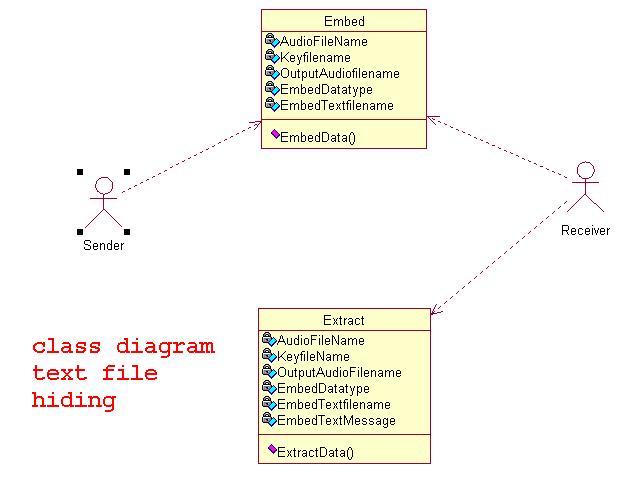
CLASS DIAGRAMS
Relationships between identified classes.