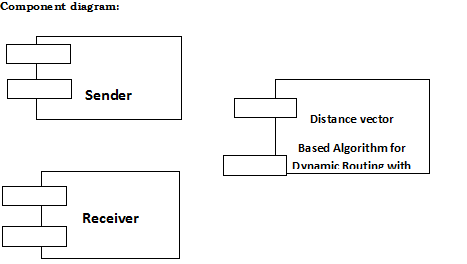
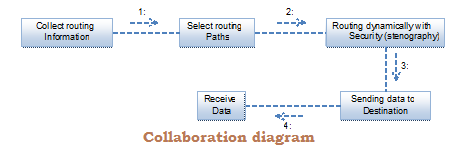
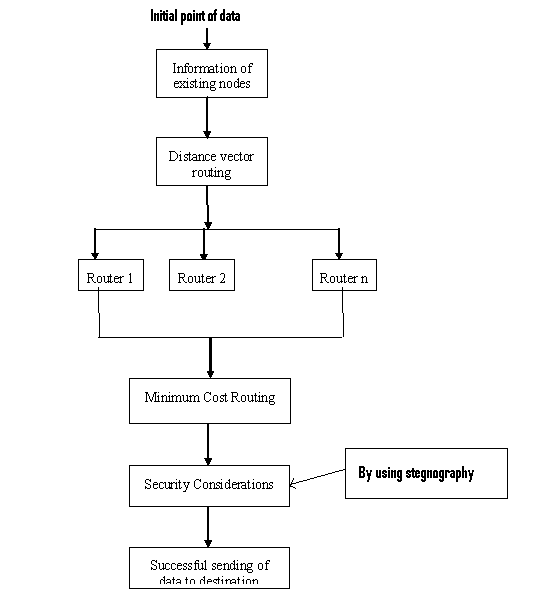
Implementation is the major phase in the software development process. I consider the Dynamic Routing with stegnography project development as the following modules:
- Network Module
- Dynamic Routing
- Randomization Process
- security enhancement module
Technologies:
To implement this stegnography Project, I consider java as the programming part and java swings is for graphical notations which can embed with different types of system configurations.
Java:
Java overview:
Most of the software companies are working hard to fulfill the client’s requirements with the best use of the resources. Clients are looking for the best performance, speed with cost management. So, the companies prefer the best technology to development of software.
To achieve the best standards companies are giving importance for the programming language such as Java. Java is a purely object oriented programming language and simple to implement the applications. Programmers feel comfortable to working on this application. The applications can be executable in any platform i.e. platform independent. These are applicable in the real time such as ATMs, PCs, smart cards, application server and embedded devices.
Java is a distributed language and very secure. The features of this language make it very popular and it useful for the next generation. We can implement the internet programs with the help of applets. It supports distributed, robust, multithreaded, portable and memory management. It is secured language with virus free. It provides web services and it allows programmers to work on quality service development and object development.
I choose java programming language to implement my project. The important factor to develop software product are data integrity, accessibility and scalability that are fulfilled by this language. I consider java with swings to make my application success with rich interface. To develop GUI (Graphical User Interface) applications of my project, I choose java swings which are more efficient and effective.
Java Swings:
In java language using swings will give you the creation of GUI (graphical user interface) application. These are applications are very effective with text boxes, tables, buttons, text field, trees, scroll bars etc. this is the latest version of the java to create GUI application before that is uses AWT (abstract window toolkit) package. This AWT package is having the classes which are needed to create the application but with the limited scope. To overcome this problem, java introduce the swings which very dynamic in behaviour.
This Paper is written & submitted by Chandu.