Introduction
This chapter focuses on the key design aspects followed in the simulation process and the key aim of this chapter is discuss all the design patterns followed and the corresponding simulation standards used in creating the simulation environment. As the main aim of this Intrusion Detection System Final Year Project is to evaluate the intruder detection across the large networks based on frequency measures, a simple mobile ad hoc network is considered as the required network and almost 30 nodes are considered in this context and the simulation is done by generating the required traffic and DSR is used the routing protocol and the actual design used is explained as below.
Simulation tool used
There are a variety of simulation tools available to simulate the mobile ad hoc networks and the key among them are OPNET modeler, OMINET and NS2 and among all these tools, OPNET provides a rich user interface for the simulation. OPNET supports many models across the simulation and also provides the scope to analyze the results using a large set of performance metrics.
Few important technologies like MANETs, Wi-Fi, ad hoc networks and wireless sensor networks can be simulated very easily using the OPNET modeler and the basic simulation model that can be developed using the OPNET modeler is as given below
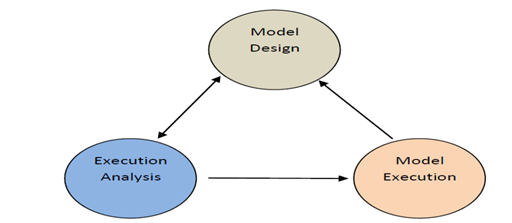
To proceed with the simulation, a perfect model design is required and once the model is created, it can be executed using the simulation process and finally the results can be analyzed. The actual software and hardware requirements for installing the OPNET are given in the appendix section.
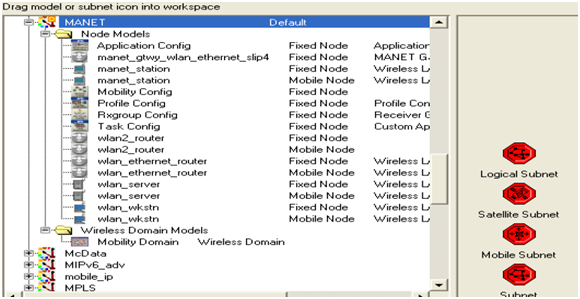
OPNET provides a rich user interface to the simulation of MANET model and even there are some default and configurable models against the MANET simulation and they can be used to create the required MANET setup very easily. OPNET provides a simple feature known as object palette and this palette can be used to drag and drop the required objects to create the MANET environment and the below figure shows the typical OPNET modeler object palette
Design of scenarios
As the main aim of this Intrusion Detection System Final Year Project is to detect the intruder actions across the networks using the frequency based metrics, three scenarios are considered in this simulation process and the key metrics used are as given below.
No attacks scenario
This is the first scenario used across the simulation and in this design, 30 mobile nodes are used and few configuration settings are done in this scenario. Following are the key nodes used across the simulation process and they are as listed below
- Mobile configuration and this node can be used to set the default mobile configuration settings for the mobile nodes considered as the simulation process
- Application configuration node and this node can be used to define the applications to be supported across the simulation process
- Profile configuration node and this can be used to set the required profiles for the application defined across the application configuration phase
- 30 mobile nodes and these nodes are configured using the wireless LAN mobile nodes that are available in the object palette as discussed in the previous section
- A fixed wireless LAN server and this server handles all the requests from the 30 mobile nodes used
Once all these nodes are dragged and dropped across the workspace of the simulation environment they require configuration settings are done to proceed with the simulation process and the corresponding screenshots for setting the configuration details are given in the appendix section. The actual simulation parameters used to setup the network are as given in this section. As discussed 30 mobile nodes are considered and MANET is chosen as the required model family.
A network scale of 1500 X 1500 square meters is considered across a campus and the simulation is done by using all the nodes as discussed in the previous section. DSR is considered as the required routing protocol and all the mobile nodes and the wireless LAN server are assigned with this routing protocol and the simulation is run for 2 minutes to get the desired results.
The basic application used in this simulation is Database application and this application generates the required traffic across the all the mobile nodes and the wireless LAN server using the DSR routing protocol and the corresponding settings are done across the application configuration node as discussed above.
This database application is chosen and the corresponding parameters are set across the simulation process to generate the required traffic and this application is supported by all the mobile nodes and the server used in the simulation process. Once the application configuration settings are done the very next step is to define the profile settings and this can be done using the profile configuration node as given in the previous section.
Required number of rows are added to the profile tab and the corresponding applications created across the application configuration level are added to the profile and this means that now a separate profile is created for the application defined and this profile is used by all the mobile nodes and the wireless LAN server to generate the required traffic against the application being used across the network.
Now once the application and profile configuration settings are done, now the actual mobile nodes and server should be configured to generate the required traffic. All the mobile nodes are selected and their attributes are edited to support the applications and profile created and the actual process is given in the simulation procedure chapter. The actual parameters used in the configuration process are as listed below
- Application destination preferences
- Application source preferences
- Application supported profiles and
- DSR routing protocol parameters
All the parameters are set against the simulation process and as this scenario deals with no attacked nodes, all the default parameters for the DSR routing protocol are used and they are varied to generate more traffic and illegal routing requests in the next two scenarios. Once the node level and the server level settings are done, the required IP Addressing is assigned to all the mobile nodes to create the required addressing scheme.
As the nodes used in the simulation process are mobile in nature, mobility is required for the nodes and this can be done by configuring the mobile configuration node as discussed in the previous section. Default random waypoint mobility is used for the simulation process and this can be done by doing some setting at the mobile configuration node and the actual settings and the corresponding procedure followed is discussed in the simulation procedure chapter. Once the required mobility is set for all the nodes across the MANET, now the performance metrics should be initiated to estimate the required results.
OPNET provides three levels of performance estimation like the global level, node level and link level. Global level metrics are used across the design of the simulation and the key metrics used to collect the results are as listed below
- Route discovery time
- Routing traffic sent in packets per second
- Routing traffic received in packets per second
- Total cache replies sent
- Total packets dropped
- Total route errors sent
All the metrics are set across the simulation process and the simulation is run for 2 minutes to gather the required results and the next scenarios used in the simulation process are as given below
Two attack nodes scenario
The actual design followed to create this scenario is similar to the first scenario and this can be achieved by just duplicating the scenario. Once the scenario is duplicated, two mobile nodes are identified and the corresponding settings are changed for the DSR routing protocols. Following are the actual parameters changes for the DSR routing protocol and in general when a node is attacked by the intruders, the corresponding routing protocol parameters are varied and more and improper traffic is generated across the network and this traffic is considered as the anomaly traffic. Following are the actual attributes of the DSR routing protocol that were changed and they are listed below
- Sending buffer parameters
- Router discovery parameters
- Route maintenance parameters
All these parameters are varied against the default values to create the anomaly traffic across the network and the actual values used to create this anomaly traffic are discussed in the simulation procedure chapter.
Three attack nodes scenario
This scenario can be created by just duplicating the second scenario and the in this case three nodes are identified as the attack nodes and the corresponding anomaly traffic is generated by these three nodes. Similar to the previous scenario, the parameters of the DSR routing protocol are changed to generate the required anomaly traffic and the same parameters as discussed in the previous scenario are changed across this simulation process.
Once all the required scenarios are created, the simulation is run for 2 minutes and similar performance metrics are used for all the scenarios as discussed above. Once the simulation is successful the results are compared against all the scenarios and the actual intruder detection is evaluated. The actual simulation procedure followed and the results achieved are explained in the later chapters of this project.
DFT implementation
As the main aim of this Intrusion Detection System MS Final Year Project is to detect the intruders across the networks using the DFT (Discrete Frequency Transformation), the attributes of the routing protocol are changed in a manner such that a DFT code is generated across the back end in C++. The number of intruder nodes are increased scenarios by scenario and the random selection done against the scenarios purely depends on the DFT equations and thus in the second scenario two nodes are selected and in the third scenario three nodes are selected as the intruder nodes and their routing protocols are changed against the DFT equations.

Sir i want to make this project. Can u help me plz??
hello sir ,i want the source code and project explanation and project implementation ,
Hello,
I want the source code and project explanation/implementantion. Thank you!