Chaotic Image Encryption Techniques Project in Java is intended to the people who need privacy for their confidential images. It was most suitable in the networking Systems, so it was more eligible in Space Science research centres.
The user can have membership by concerning the administrator. The system dynamically generates member id on presenting the user details. The user can have transactions by having their member id. The user adds the image for encryption and encrypts it for confidential images.
Chaotic Image Encryption Techniques Project Users:
1. Administrator.
2. User.
3. Other (Guests).
Administrator:
Administrator is having all the rights to access this portal. Admin can view all the images, and the status of the encrypting and decrypting process. He will have control over the network whether to accept the server‟s request for receiving image. He will provide all the benefits for image encryption and decryption.
User:
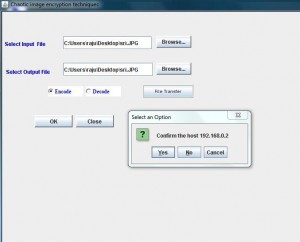
The people who use this system for providing security for confidential images are users. There may be different set of users for this system. The users just load an image to encrypt and encrypt it and enter the destination systems IP address to transfer the image and he can view the status of the network for the sent image.
Guests:
Guest or the new user can only view the functionalities in the portal and they have no access permissions unless they are registered.
Proposed System
Proposed system provides a solution to existing system by extending its facilities. The proposed study aims to explore the possibility of using chaotic or chaos-based encryption techniques to protect remote sensing satellite images and provides high level of security in efficient and reliable way.
Chaos based cryptographic scheme provides high security level, less computational time and power in reliable and efficient way to deal with balky, difficult and intractable data that why many researchers recommends that it is more suitable for multimedia data, especially for images. Chaos-based system have many properties to achieve high security level, such as sensitivity to change initial conditions and parameters, periodicity (a system that tends in probability to a limiting form that is independent of the initial conditions), random behavior and unstable periodic orbits with long periods. It has very high diffusion and confusion properties that are desirable for cryptosystem.

Hi,
I need source code for Keyless image encryption can I get?
Thanks and regards
now do u have keyless image encryption method
i need the source code…please
i need source code for this project.
need source code..plss
Can you please send java code to this email address
Can you send the source codes ASAP?
source code …please !!
Please send the source code !!
i really need this …
Sir can you please send me the source code of image encryption project on my email id.
can u please send me the source code
Can you send the source code to my email?
I need the source code
Would you send me source code …please ?
Please i need the source code plzzzzz send it to me 🙁
i need source code
Can you send the source code to my email?
Can you send the source code to my email? Plese
I need source code
I hace source code…..can any let me know step by step procedures after project got run…..selection of image n after that….
I have source code…..can any let me know step by step procedures after project got run…..selection of image n after that….
hello can i have that source code .plz mail me at [email protected]
Please can you send me the source code?
Can you send the source code to my email?